That gap is how breaches happen.
TrustStrike closes it - continuously, automatically.
TrustStrike Monitor is an enterprise external attack surface management (EASM) platform built around how attackers actually map a target. Continuously discovers every internet-facing asset - subdomains, APIs, cloud, mobile, social - then unifies vulnerability scanning and brand-impersonation monitoring into a single live feed.
Every asset, vulnerability, and lookalike domain - live, continuously scanned.
Assets, vulnerabilities, brand threats, and trends. Your security posture, updated continuously and surfaced at a glance.
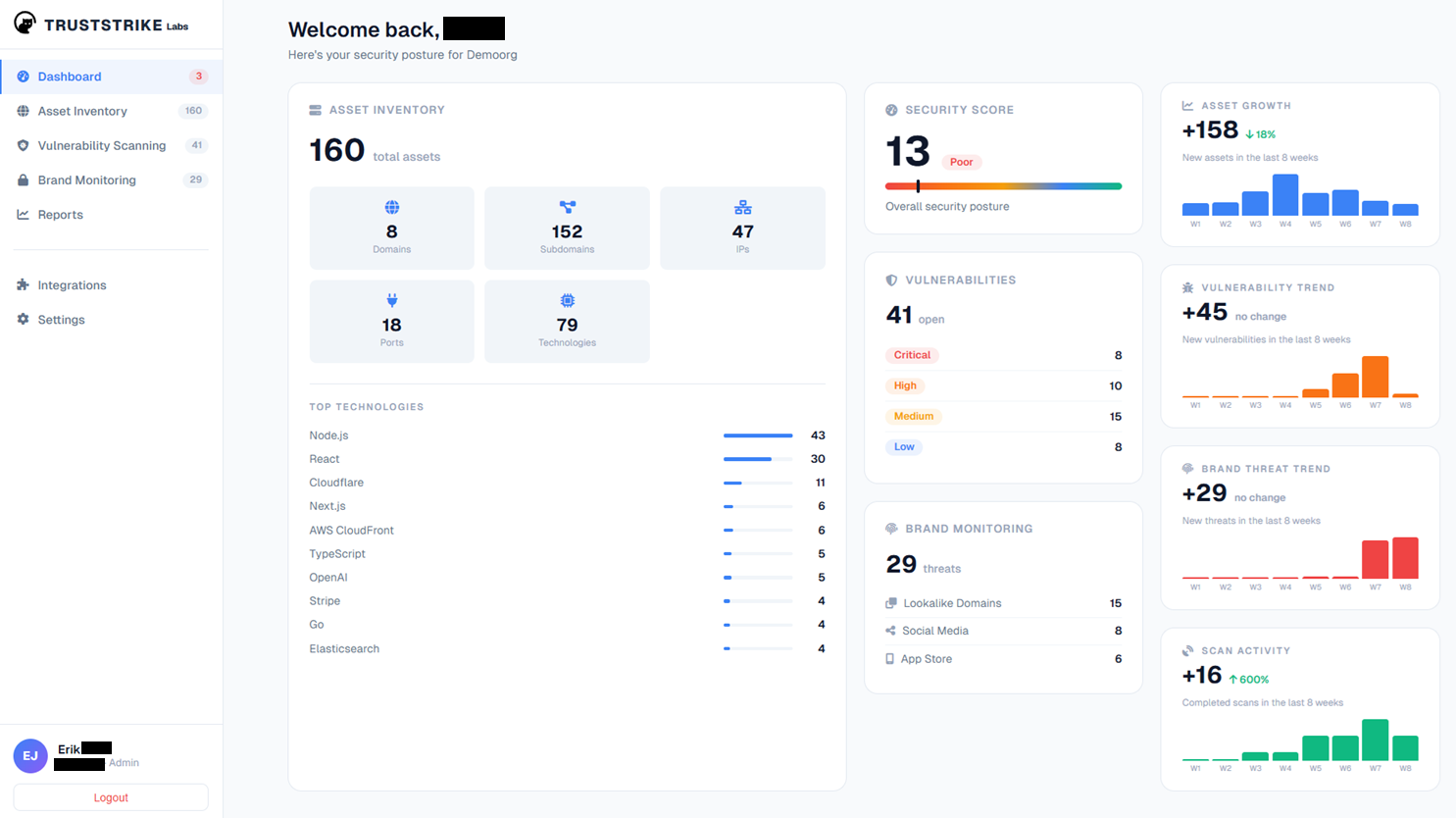
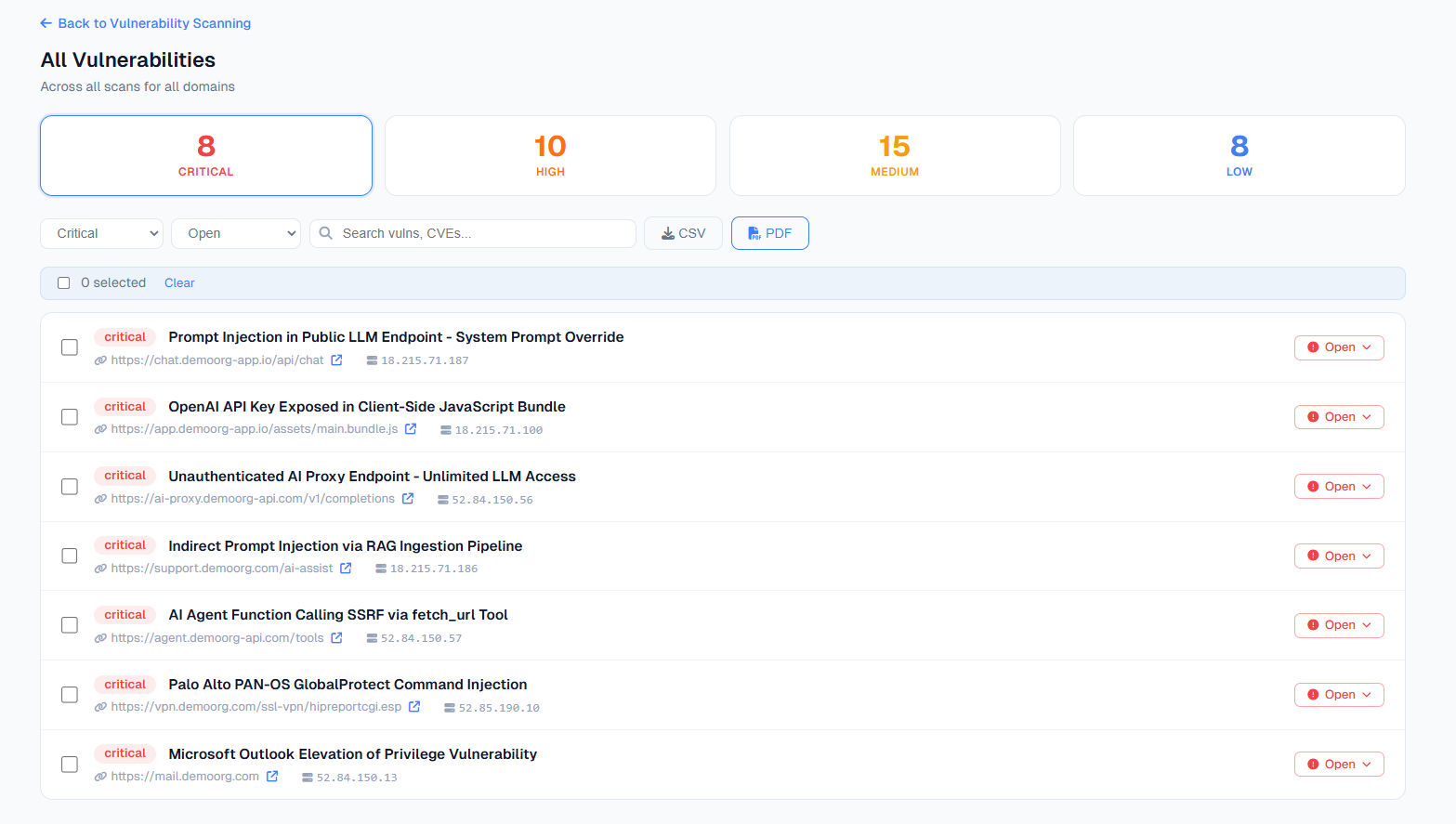
41 vulnerabilities tracked across your surface. Prioritized by exploitability, not just CVSS score. Know what attackers would reach for first.
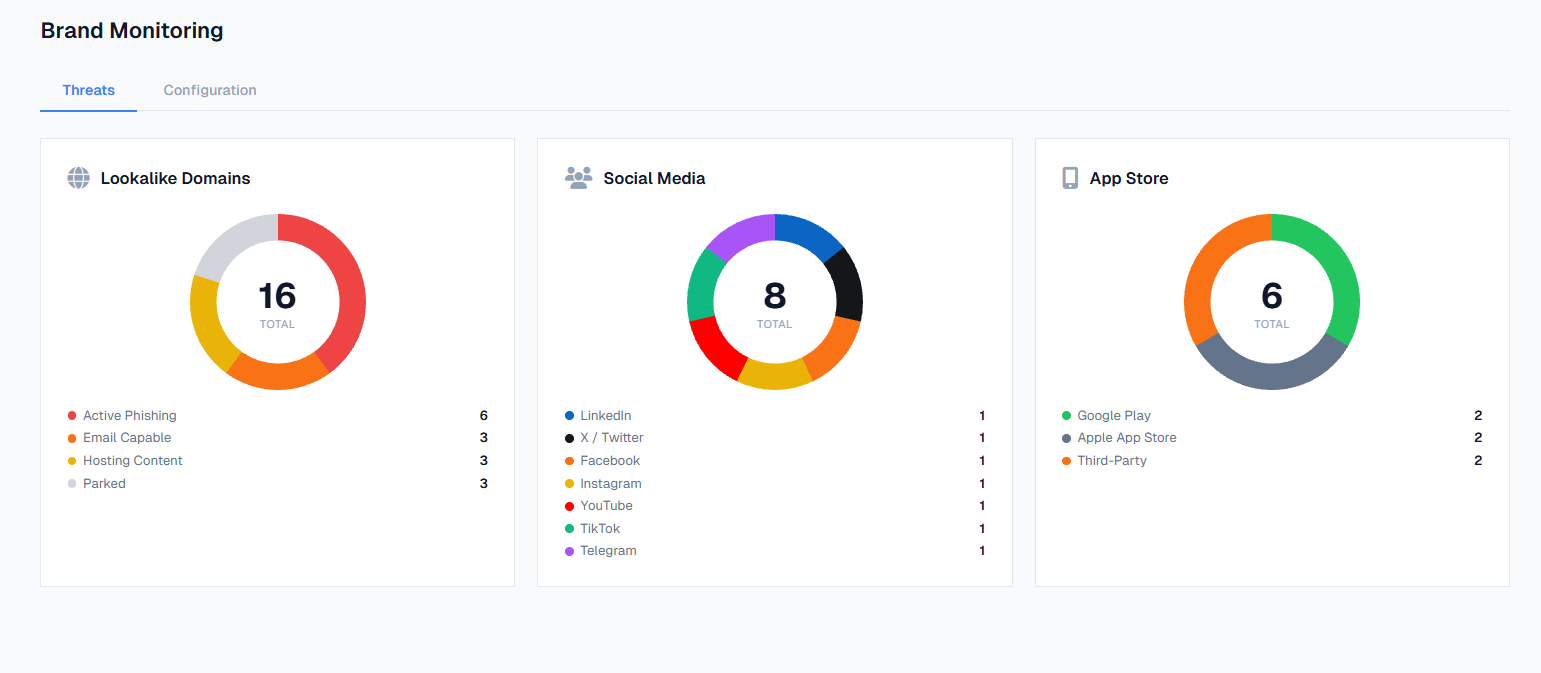
29 threats detected: 15 lookalike domains, 8 fake social profiles, 6 App Store copycats. Your brand, continuously watched.
See TrustStrike Monitor in action with a personalized demo.